Protecting Stockpiles of Deadly Weapons: High Security for a Safer World

5 out of 5
| Language | : | English |
| File size | : | 10853 KB |
| Screen Reader | : | Supported |
| Print length | : | 32 pages |
In a world where the threat of terrorism and other forms of violence is ever-present, it is essential to take steps to protect the stockpiles of deadly weapons that are held by governments and other organizations. These weapons have the potential to cause immense harm if they fall into the wrong hands, and it is therefore imperative to implement stringent security measures to prevent this from happening.
The Importance of High Security
The consequences of a terrorist or other criminal organization gaining access to a stockpile of deadly weapons can be catastrophic. These weapons could be used to carry out mass shootings, bombings, or other attacks that could result in the deaths of countless innocent people. In addition, the theft of these weapons could also lead to the proliferation of nuclear or other weapons of mass destruction, which would pose a grave threat to global security.
For these reasons, it is essential to implement high-security measures to protect stockpiles of deadly weapons. These measures should be designed to deter potential attackers, detect unauthorized access, and respond quickly to any security breaches.
Physical Security Measures
Physical security measures are the first line of defense in protecting stockpiles of deadly weapons. These measures include:
- Fencing and walls: Stockpiles should be surrounded by high fences or walls that are topped with barbed wire or other security features.
- Gates and checkpoints: All entrances to the stockpile should be controlled by gates and checkpoints that are manned by armed guards.
- Lighting: The stockpile should be well-lit at all times to deter potential attackers and make it easier to detect unauthorized access.
- Surveillance cameras: The stockpile should be monitored by a network of surveillance cameras that are linked to a central security station.
Electronic Security Measures
Electronic security measures can be used to complement physical security measures and provide additional layers of protection. These measures include:
- Intrusion detection systems: These systems use sensors to detect unauthorized entry into the stockpile. When an intrusion is detected, an alarm is triggered and security personnel are dispatched to investigate.
- Motion detectors: These devices detect movement within the stockpile and can be used to trigger an alarm or alert security personnel.
- Access control systems: These systems control who is allowed to enter the stockpile and can be used to track the movement of personnel within the facility.
Armed Security Personnel
Armed security personnel are an essential part of any high-security system. These personnel are responsible for guarding the stockpile, responding to security breaches, and apprehending any unauthorized individuals who attempt to gain access to the facility.
Security personnel should be trained in the use of firearms and other weapons, as well as in the tactics of охрана and counterterrorism. They should also be familiar with the stockpile's security measures and procedures.
Emergency Response Plans
In the event of a security breach, it is essential to have a well-coordinated emergency response plan in place. This plan should outline the roles and responsibilities of all personnel involved in the response, as well as the procedures for notifying law enforcement and other authorities.
The emergency response plan should also include procedures for evacuating personnel from the stockpile and for securing the facility against further attack.
Protecting stockpiles of deadly weapons is a complex and challenging task that requires a multi-layered approach. By implementing a combination of physical security measures, electronic security measures, armed security personnel, and emergency response plans, governments and other organizations can help to keep these weapons out of the wrong hands and ensure the safety of their communities.
5 out of 5
| Language | : | English |
| File size | : | 10853 KB |
| Screen Reader | : | Supported |
| Print length | : | 32 pages |
Do you want to contribute by writing guest posts on this blog?
Please contact us and send us a resume of previous articles that you have written.
 Book
Book Novel
Novel Page
Page Chapter
Chapter Text
Text Story
Story Genre
Genre Reader
Reader Library
Library Paperback
Paperback E-book
E-book Magazine
Magazine Newspaper
Newspaper Paragraph
Paragraph Sentence
Sentence Bookmark
Bookmark Shelf
Shelf Glossary
Glossary Bibliography
Bibliography Foreword
Foreword Preface
Preface Synopsis
Synopsis Annotation
Annotation Footnote
Footnote Manuscript
Manuscript Scroll
Scroll Codex
Codex Tome
Tome Bestseller
Bestseller Classics
Classics Library card
Library card Narrative
Narrative Biography
Biography Autobiography
Autobiography Memoir
Memoir Reference
Reference Encyclopedia
Encyclopedia Shirly Hook
Shirly Hook Frank Nappi
Frank Nappi Tony Rose
Tony Rose Simone Edwards
Simone Edwards Seyyed Hossein Nasr
Seyyed Hossein Nasr William Walker Atkinson
William Walker Atkinson Walt Kelly
Walt Kelly Sadie Lake
Sadie Lake Vanessa Riley
Vanessa Riley Eva Charles
Eva Charles Samantha Rodman
Samantha Rodman Stephanie T Mcrae
Stephanie T Mcrae Wahida Clark
Wahida Clark Victoria Wilson
Victoria Wilson T A Barron
T A Barron Leslie T Chang
Leslie T Chang Steven M Gillon
Steven M Gillon Terry Hill
Terry Hill Elizabeth Anne Wood
Elizabeth Anne Wood Steve Chandler
Steve Chandler
Light bulbAdvertise smarter! Our strategic ad space ensures maximum exposure. Reserve your spot today!

 Javier BellJourney Through the Social Life of a Girl on the Autism Spectrum: Navigating...
Javier BellJourney Through the Social Life of a Girl on the Autism Spectrum: Navigating...
 Russell MitchellLove Yourself and It Doesn't Matter Who You Marry: A Guide to Finding True...
Russell MitchellLove Yourself and It Doesn't Matter Who You Marry: A Guide to Finding True... Tom HayesFollow ·19.8k
Tom HayesFollow ·19.8k Peter CarterFollow ·18.8k
Peter CarterFollow ·18.8k Caleb CarterFollow ·5.6k
Caleb CarterFollow ·5.6k DeShawn PowellFollow ·4.7k
DeShawn PowellFollow ·4.7k Howard PowellFollow ·19.2k
Howard PowellFollow ·19.2k Garrett PowellFollow ·4.3k
Garrett PowellFollow ·4.3k Cruz SimmonsFollow ·11.2k
Cruz SimmonsFollow ·11.2k Amir SimmonsFollow ·16.2k
Amir SimmonsFollow ·16.2k
 Donald Ward
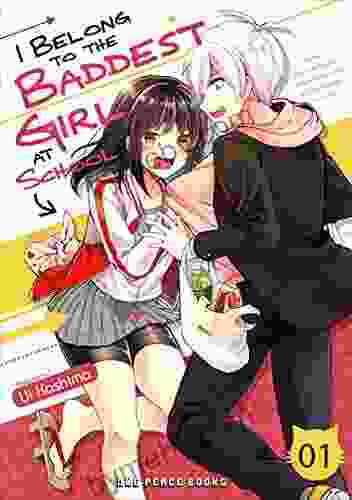
Donald WardUnveiling the Enthralling World of "Belong to the Baddest...
In the vibrant and...
 José Martí
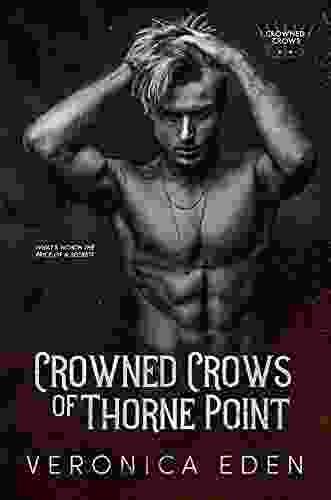
José MartíCrowned Crows of Thorne Point: A Literary Odyssey into...
In the realm of literary masterpieces,...
5 out of 5
| Language | : | English |
| File size | : | 10853 KB |
| Screen Reader | : | Supported |
| Print length | : | 32 pages |